The Personal Data Protection Law in the UAE has brought a dramatic change in rules for legal services. Before its introduction, the traditional cloud models may leak metadata across borders, leading to hidden liabilities. But in 2026, for CISOs UAE’s government now wants total data containment without sacrificing the agility of the cloud.
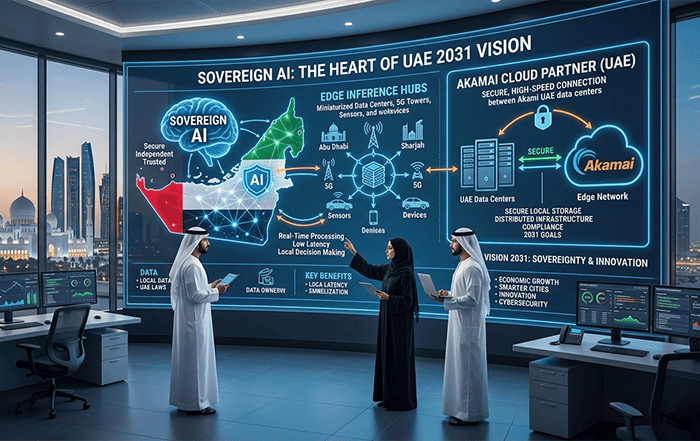
Here comes Akamai, which solves this by decentralizing the cloud itself. We are your Akamai cloud hosting partners who can bring the infrastructure to the data, not the other way around. Aim? Each byte stays exactly where the law demands.
Liability Shielding: It will remove the risk of foreign judicial access by localizing the entire management plane.
Architectural Edge: It will turn regulatory burdens into a streamlined, high-availability asset for your firm.
Does your cloud architecture violate articles 22 & 23?
For every C-Suite, the legal trap is how the data travels. In Articles 22 and 23 of the PDPL, you can strictly see the regulation and governance of cross-border movement.
While a lot of hyperscalers promise a “UAE Region,” their backplanes often leak metadata or logs to global hubs for “platform health.” For a regulator, this passive leakage equals an unauthorized transfer.
For BFSI, danger exists in the gap between residency and sovereignty. If the “master keys” to your infrastructure are with a foreign entity, your data will automatically remain within reach of foreign warrants like the U.S. CLOUD Act. But true compliance means an architecture where the management plane is as localized as the servers.
Strategic comparison: Traditional cloud vs. Akamai distributed sovereignty
Next, we need to get into the technicalities. But before that, let’s see why “standard” cloud setups often fail the PDPL litmus test for high-stakes sectors like banking and law.
- Management Plane Isolation: Most clouds use global consoles that pull local UAE data into international jurisdictions for simple administrative tasks.
- The Telemetry Trap: System logs and performance metrics often bypass geofencing, sending identifiable patterns to overseas analytics engines.
- Extra-Judicial Reach: Sovereignty is void if a foreign parent company can be compelled to hand over UAE-hosted data via international subpoenas.
- Latency vs. Compliance: Centralized hubs in neighboring countries might offer proximity, but they lack the legal protections of staying strictly within the federation.
- Automated Governance: Moving from manual configuration, where human error leads to leaks, to a “Compliance-by-Design” model that enforces residency at the code level.
| Compliance Dimension | Legacy Centralized Cloud (Hyperscaler) | Akamai Distributed Cloud (UAE-Native) |
|---|---|---|
| Data Localized Control | Regional “zones” with global management overhead. | Hard-fenced UAE instances with 100% local data-plane retention. |
| Cross-Border Metadata | Telemetry and logs often exit the jurisdiction for “platform health.” | Zero-egress telemetry; logs stay within the UAE domestic boundary. |
| Judicial Exposure | Subject to foreign subpoenas via global HQ (e.g., US CLOUD Act). | Decoupled legal entity structure, shielding data from extra-judicial reach. |
| Latency & Performance | Round-robin routing through regional hubs (e.g., Bahrain/Europe). | Edge-local processing within the UAE’s domestic telco fabric. |
| Processor Accountability | Shared responsibility model with high “customer-side” configuration risk. | Managed “Compliance-by-Design” at the infrastructure and edge layer. |
How Akamai’s Distributed Fabric Guarantees 100% Residency
Most cloud providers talk about regions, but they still move data behind the scenes. Akamai’s distributed fabric is different because it pushes the actual compute power to the UAE’s local ISP level.
When a bank processes a transaction, the PII stays on domestic nodes. It never “phones home” to a global hub in another country. Using Akamai cloud services at the edge means the data never crosses a border during active processing. It stays exactly where the law says it should.
We also solve the “backdoor” problem with geofenced management. By locking the administrative access, it works only from authorized UAE IP ranges. It further creates a sovereign bubble around your data. So your backups stay localized within the federation, protected by Akamai cloud security. It blocks threats before they even reach your core network.
The Legal Counsel’s Checklist: Auditing the Data Lifecycle
Meeting the PDPL requirement is about how you manage data over time. For instance, Article 6 makes consent withdrawal a major headache for legal teams.
Our architecture uses local API triggers to purge data instantly within the UAE. So, as a client exercises their “right to be forgotten,” it happens immediately, and the data doesn’t leave the jurisdiction. It’s clean, fast, and fully compliant.
Another pressure point is Article 9. It requires breach notifications within 72 hours. Since we monitor locally, your team gets a clear view of any issues instantly.
Next, we simplify Article 16. As an Akamai cloud service, we make data portability a purely domestic operation. This avoids “egress traps” where your data is accidentally routed through international scrubbing centers during a transfer.
Future-proofing for 2026
If we see the current regulatory climate in the UAE, “close enough” isn’t enough for the legal and financial sectors. Moving to a distributed, sovereign cloud is turning into a necessity that hardens your infrastructure against global instability and foreign judicial reach. When you pick the right architecture design for the PDPL, it moves you from reactive defense to proactive leadership.
Want to secure your data in the UAE? You need a professional partner to move through these technical-legal overlaps.
We are right here! Contact Codelattice at askus@codelattice.com for a free consultation or contact us for more information on how we can future-proof your compliance strategy.